Mondoo 6.9 is out!
🥳 Mondoo 6.9 is out! This release includes new Kubernetes pod scanning and top CVEs in the space overview!
Get this release: Installation Docs | Package Downloads | Docker Container
🎉 NEW FEATURES
Top Platform Vulnerabilities on Overview
Problem: You want to find the critical CVEs in your environment quickly
Solution: The Mondoo Overview page now shows your space's top five platform vulnerabilities. This new view lets you quickly determine the most impacting vendor advisories and how many assets are affected by each advisory. The individual advisories link to detailed information pages summarizing the included CVEs and impact. You can also select View All to see all security advisories in your space.
Kubernetes Pod Scanning
Problem: You have hundreds or even thousands of different workloads in your Kubernetes clusters, and you want to see the security status of individual workloads instead of just the cluster as a whole.
Solution: This week, we're shipping our first slice of Kubernetes resource scanning with pod scanning. With this new discovery mode, each pod in your cluster becomes an asset within Mondoo. Policies are applied at the pod level, and you can write MQL queries against these pods instead of the whole cluster. This gives you more granular workflow scanning and improved alerting.
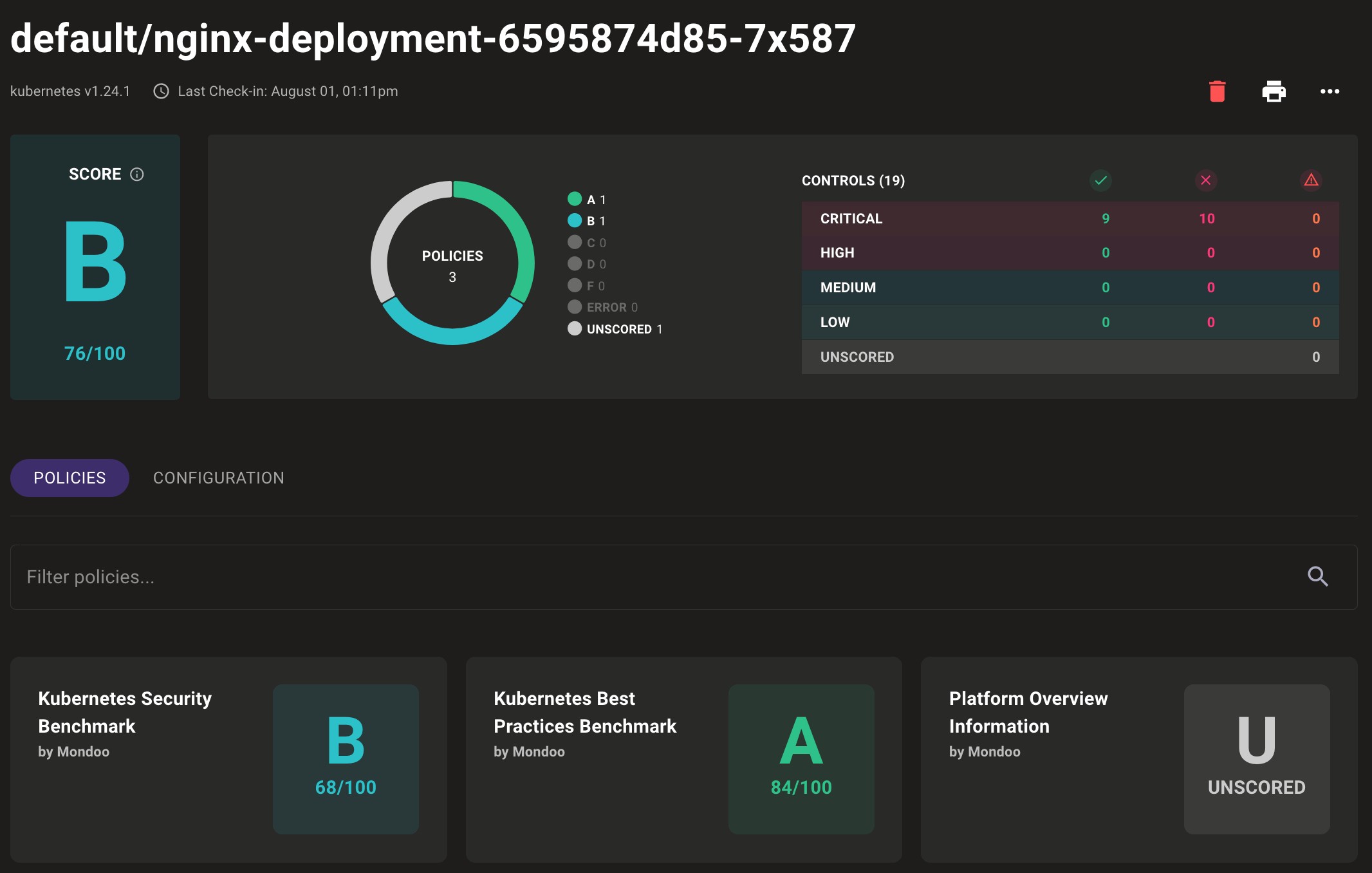
To start scanning discovery pods as assets during your Kubernetes scans, run mondoo scan k8s --discover pods.
Stay tuned for next week's release when we introduce more new Kubernetes resources as Mondoo assets, along with new out-of-the-box policies for scanning these assets.
Mondoo Kubernetes Operator 1.0
We started our open source Mondoo Operator for Kubernetes project in January of this year. Since then, the Mondoo team has been busy extending the functionality, ensuring stability, and squeezing every ounce of performance out of the codebase. This week after 300 pull requests merged, we shipped the 1.0 release.
What does 1.0 mean for me?
1.0 means we're confident in the functionality and stability of the project. Additionally, since Mondoo follows Semantic Versioning, we won't intentionally break any configuration interfaces in subsequent 1.x releases. Config stability between minor releases makes upgrades easier without requiring stepped upgrades.
If you're still on an older Mondoo Operator release, we strongly encourage you to upgrade to 1.0. We've introduced significant new capabilities over the last few months, including pod container image scanning, rootless/read-only execution, and CronJob-based scanning. See our Mondoo Operator Upgrade documentation for more information on upgrading to 1.0.
🧹 IMPROVEMENTS
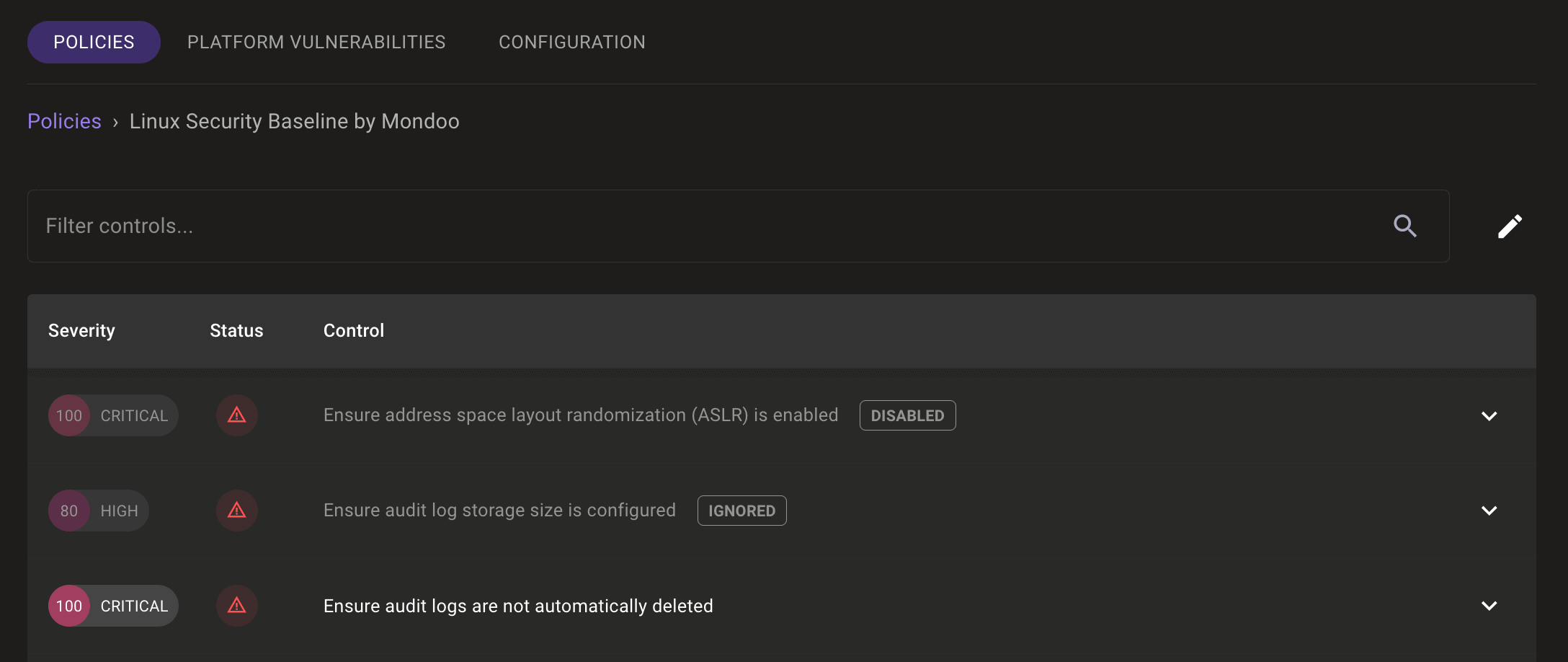
Show Disabled and Ignored Controls
Disabled and Ignored controls in policies are now visually indicated in assets' policies, making it clear which policies impact scoring.
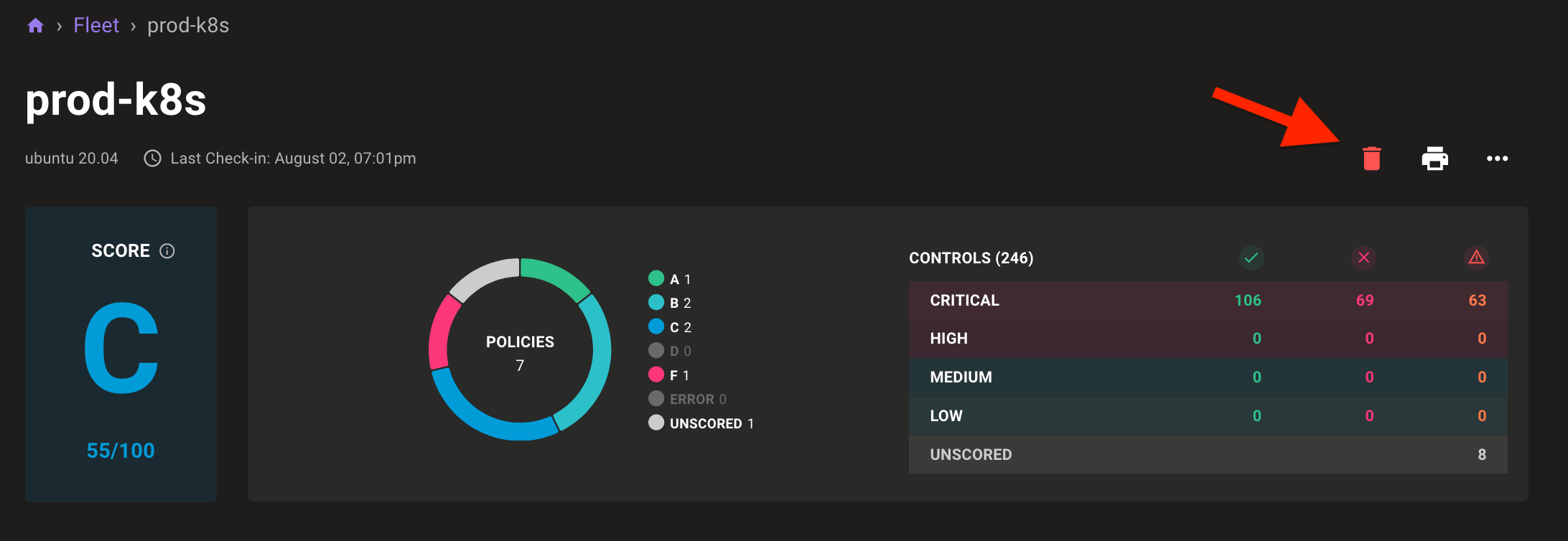
Simpler Asset Deletion
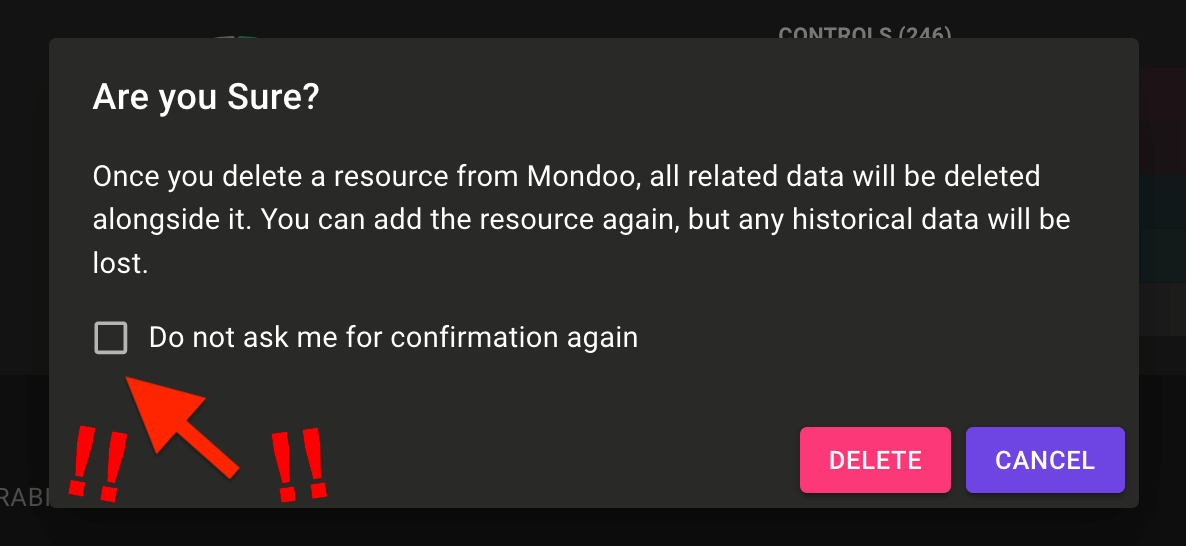
You can now delete assets directly on the asset page by selecting the delete icon.
If you're one to live dangerously, you can even opt out of warnings and delete assets with just a single selection.
Improved Linux EOL Detection
We've improved the EOL operating system detection in Mondoo Client to support the following new Linux releases:
- Alpine 3.16
- openSUSE 15.4
- Oracle Linux 9
- Rocky Linux 9
- SUSE Linux Enterprise 15.4
MQL Improvements
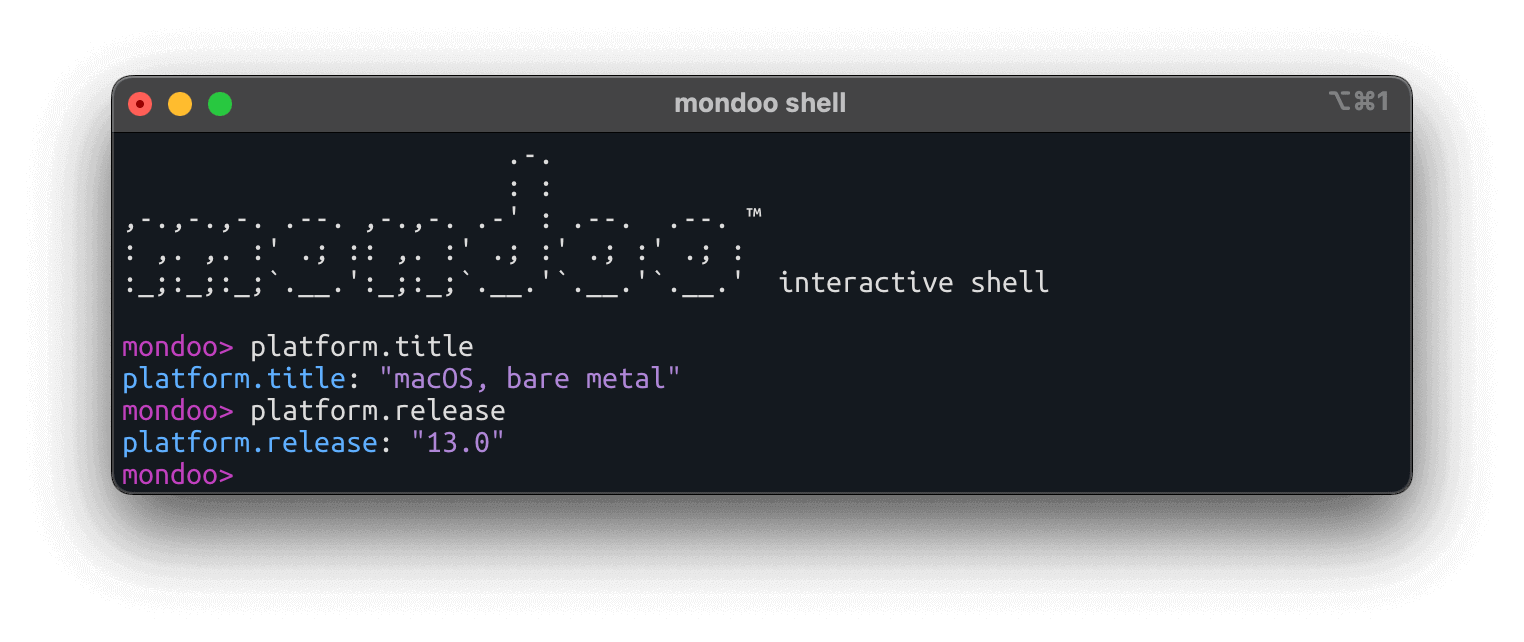
We've updated MQL's platform resource to improve gathering information on assets. A new platform.title value exposes a human-friendly version of the platform's name, and the platform.version value has been deprecated in favor of platform.release.
🐛 BUG FIXES AND UPDATES
- Resolves incorrect EOL dates for Rocky Linux 9 and SLES 15.3.
- Adds a timeout for long running Kubernetes Operator scans.
- Updates the VMware Appliance from Debian 11.2 to 11.4 to resolve CVEs in the underlying Debian installation.
- Resolves failures during container image scanning.
- Resolves failures during Terraform config file scans.
- Resolves failures during EBS volume scans.
- Remove references to "asset" in CI/CD run scan pages.
- Client Linux Security Baseline's control 'Ensure / and /home are encrypted' now executes correctly on btrfs formatted partitions.
- Users with the Mondoo viewer role can now list ChatOps integrations
