Mondoo 8.9 is out!
🥳 Mondoo 8.9 is out! This release includes expanded EOL/CVE data, expanded asset inventory capabilities, and more!
Get this release: Installation Docs | Package Downloads | Docker Container
🎉 NEW FEATURES
Alpine 3.17 and Ubuntu 23.04 CVE data
In addition to EOL information, Mondoo now reports CVEs in Alpine 3.17 and Ubuntu 23.04 packages. Container image and Kubernetes cluster scans now automatically expose CVEs in your images.
Asset inventory data out of the box
When you create a new space, all Mondoo query packs are enabled by default so you can dive right into the asset resource explorer without needing to first enable query packs. This extends out-of-the-box asset inventory data to:
- Windows
- macOS
- AWS
- Azure
- GCP
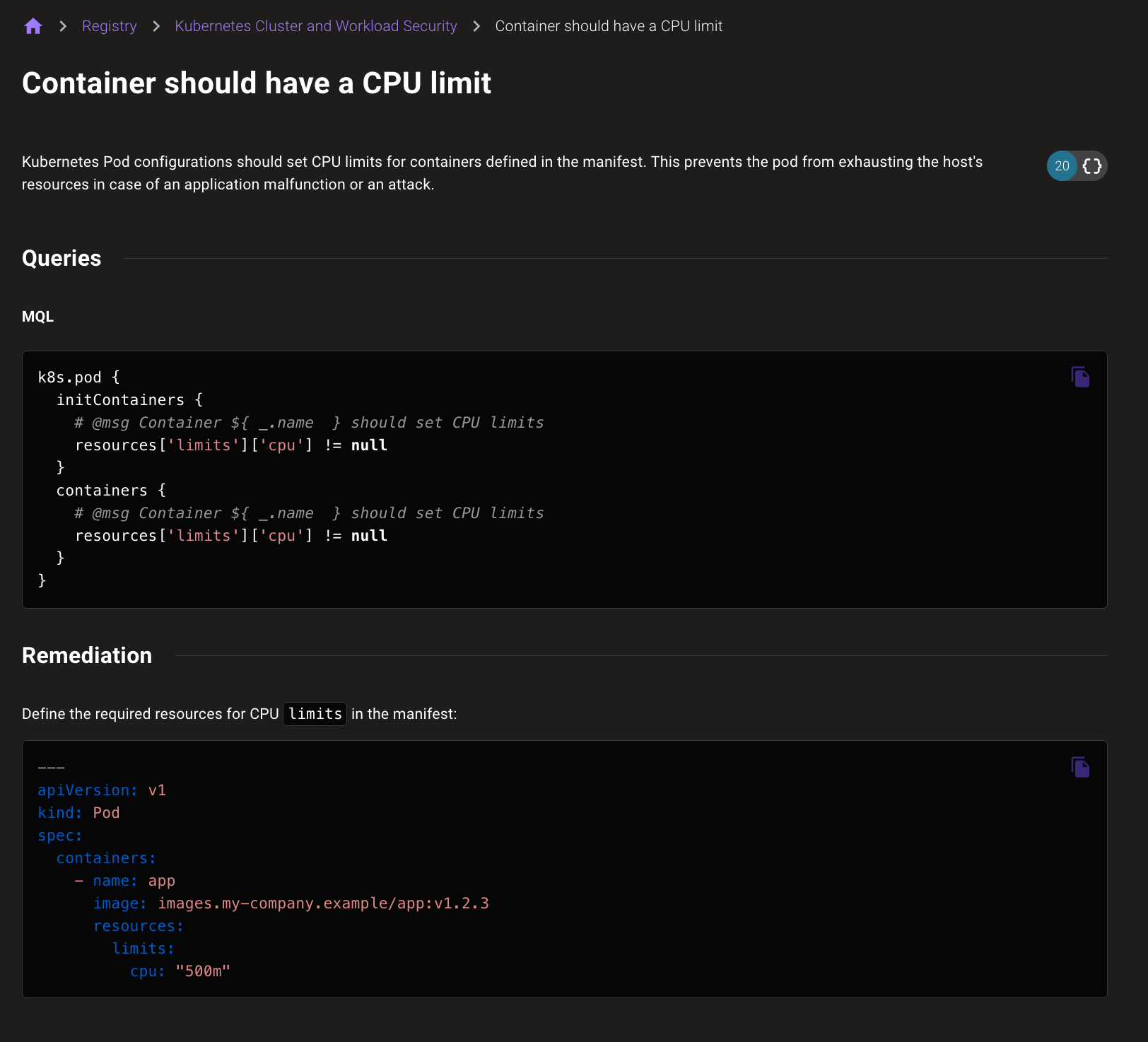
Dive into queries more easily
Sometimes it was difficult to view or share information on queries in policies. To make diving into policies and sharing those findings easier, we've given queries their own pages. View everything you need to know on a single page and share those findings with a URL that goes right to the query.
🧹 IMPROVEMENTS
Improved UI performance
Everyone loves a snappy UI, so we've worked behind the scenes to make sure space and asset pages load as quickly as possible. In some cases pages will load 10x faster than last week.
Updated VMware Photon EOL data
On May 2, VMware announced the Photon 5.0 release and at the same time clarified the EOL dates for Photon 3.0 and 4.0. Mondoo now includes this updated EOL data along with support for detecting Photon 5.0.
Updated query packs and compliance policies
- All Kubernetes query packs have been merged into a single pack that's simpler to enable and applies automatically to all assets in your clusters.
- The VMware vCenter Incident Response Pack now fetches the state of all services on ESXi hosts, not just those that are running.
- The CIS Google Kubernetes Engine (GKE) Benchmark and CIS Google Cloud Platform Foundation Benchmark policies now fail with an impact score of 95 if a default service account is used on a GKE cluster.
- The Amazon Web Services (AWS) Best Practices for NIST 800 171 policy now includes impact scores, descriptions, and remediation steps for all queries.
- Update the CIS
Ensure loopback traffic is configuredquery to also check that firewall packages are installed. - Update the CIS
Ensure default deny firewall policyandEnsure password reuse is limitedqueries for SLES hosts. - Fix false positives in the CIS
Ensure default deny firewall policyquery when using nftables.
🐛 BUG FIXES AND UPDATES
- Fix a panic when running
cnspec bundle lint. Thanks for reporting this, @kmf! - Improve the wording of the prompt to send the scan reports to Mondoo's reporting service.
- Fix failures fetching more than 100 repositories in the GitHub provider.
- Fix failures scanning vSphere switches if there are no defined uplinks.
- Fix failures in the JSON output formatter if the asset could not be scanned.
- Update more error messages from the legacy
transportwording to the correctproviderwording. - Fix failures querying data from the
aws.cloudtrailresource. - Optimize the AWS integration Lambda functions to consume fewer API calls.
- Fix queries on assets not showing as disabled or ignored.
- Update the checks count on the assets page to reflect the actual number of enabled checks, not just those available to run.
