Mondoo 6.7 is out!
🥳 Mondoo 6.7 is out! This release includes a pile of new policies and policy updates
Get this release: Installation Docs | Package Downloads | Docker Container
🎉 NEW FEATURES
Summary Scan Output
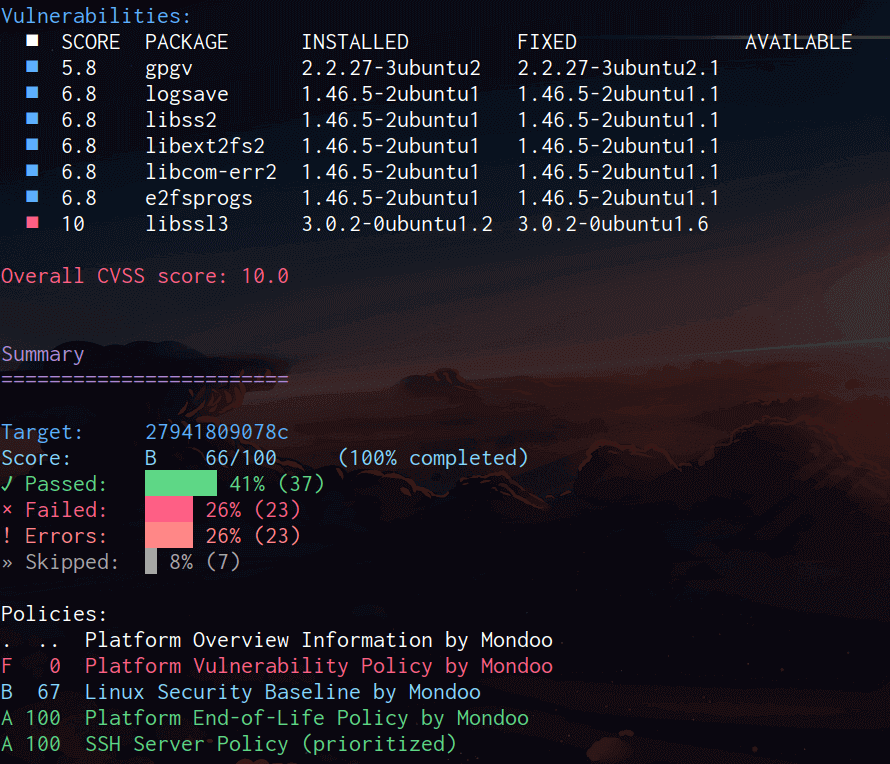
Problem: Mondoo scans print all results for every query in the CLI. However, sometimes users just want to see a quick summary of how the scan went, especially when it's collected upstream for a deeper analysis.
Solution: Mondoo now includes a new summary output mode. This mode contains just the summary portion of the Mondoo scan so you can quickly determine the security posture of systems.
NSA PowerShell Policy
Problem: Mondoo has always provided comprehensive resources for Microsoft PowerShell, but we never shipped a policy for its security best practices. This forced users to research, author, and maintain their own PowerShell policies.
Solution: Mondoo includes a new PowerShell security policy NSA PowerShell: Security Measures to Use and Embrace. This policy implements the recommendations of the United States, New Zealand, and the United Kingdom cybersecurity agency's whitepaper Keeping PowerShell: Security Measures to Use and Embrace.
Time Synchronization Policy
Problem: You want to ensure accurate time across systems within your organization for authentication and logging purposes.
Solution: Mondoo now includes a new Operational Best Practices for Time Synchronization by Mondoo policy for macOS, Linux, and Windows hosts to ensure that systems are correctly syncing their time.
Bundesamt für Sicherheit in der Informationstechnik (BSI) Policy
Problem: You want to secure your Debian- and Red Hat-based Linux systems according to the Federal Office for Information Security (BSI) and pass a BSI audit.
Solution: Mondoo now includes a new BSI SYS.1.3 Linux and Unix Servers by Mondoo policy. BSI is a German standard for IT security, similar to SOC 2 in the US. We are releasing this first policy with support for Debian- and Red Hat-based Linux to ensure that systems are correctly hardened according to the BSI requirements. This is especially helpful for users in the DACH region overall and Germany in particular.
macOS Ventura (13) support
Problem: Apple is currently working on the next major version of its Mac operating system: macOS Ventura (release 13). It is slated for a release towards the end of this year. An early version of this new release is now available in beta and can be used today. However, the Mondoo baseline policy did not support it yet.
Solution: Mondoo Client has been tested on macOS Ventura beta and the macOS Security Baseline by Mondoo policy has been updated for this upcoming release.
New Kubernetes MQL Resources
Solution: Mondoo now includes new StatefulSet and ReplicaSet resources so you can write policies for these resource types.
🧹 IMPROVEMENTS
Improved Linux Policies
Solution: Mondoo's Linux Baseline policy and various CIS Linux policies have been updated for improved reliability and to better secure your systems:
- New:
Ensure sudo logging is enabledcontrol added to Mondoo Linux Security Baseline - Bugfix:
Ensure SSH access is limitednow passes if SSH access is limited using onlyAllowUsers/AllowGroups - Bugfix: Failures running
Ensure all GIDs in /etc/passwd exist in /etc/grouphave been resolved - Bugfix: Improved reliability in
Ensure that strong Key Exchange algorithms are usedandEnsure only strong MAC algorithms are usedcontrol - Improved: Impact scores added to many controls
- Improved:
Ensure permissions on bootloader config are configuredcontrol now checks that the file is owned by root/root - Improved:
Ensure permissions on /etc/motd are configuredcontrol now checks that the file is owned by root/root - Improved:
Ensure permissions on /etc/issue are configuredcontrol now checks that the file is owned by root/root - Improved:
Ensure permissions on /etc/issue.net are configuredcontrol now checks that the file is owned by root/root - Improved:
Ensure permissions on all log files are configurednow shows which log files do not have the proper permission in the output - Bugfix: Fix errors running
Ensure automatic mounting of removable media is disabled - Bugfix: Improved compatibility with Debian in
Ensure access to the su command is restricted - Improved:
Define the hardened ciphers for all SSH configurationscontrol now better runs on RHEL-derivative distros - Bugfix: Improved compatibility with Debian/Ubuntu in
Define the hardened ciphers for all SSH configurations - Improved:
Ensure permissions on all log files are configurednow includes remediation steps to ensure future log files have the correct permissions - Improved:
Ensure SSH root login is disabledcontrol now allowsprohibit-passwordvalue - Improved: Improved compatibility with Arch Linux derivatives
- Bugfix: Fix false positives in
Ensure journald is configured to compress large log filescontrol
Improved K8s Application Policy
Problem: Your Kubernetes workloads include not just Pods, but many other kinds of Kubernetes resources. Mondoo's Kubernetes Application Benchmark scans only Pods, missing the root cause of many security misconfigurations.
Solution: The Kubernetes Application Benchmark by Mondoo now scans not just Pods, but also StatefulSets, DaemonSets, Jobs, CronJobs, and Deployments, ensuring all the resources on your cluster are secured. With these additional queries and expanded audit instructions in the policy, you can more easily find the parent resource with the identified misconfiguration, saving you time securing your cluster.
Improved Kubernetes Operator
Solution: The Mondoo Operator for Kubernetes has been improved to increase the security and performance of scanning. The operator now runs all Mondoo Client containers without root privileges for increased security. The operator's admission controller also now runs scans ~30% faster, while reducing memory consumption in the cluster.
🐛 BUG FIXES AND UPDATES
- Resolves inconsistent results when scanning Kubernetes manifests using
mondoo scanvs. Mondoo Operator admission controller scans - Resolves failures running scans on Windows systems with the system language set to German
- Resolves failures scanning Azure when the current stack is not set
- Resolves two failures in MQL that could result in inconsistent or incorrect results
- Provide user friendly error messages when scanning container images in private registries
- Improved readability within policy results
- Wrap long asset names in the fleet view and the asset pages
