cloud-init and Mondoo
This page covers how to use cloud-init to install cnspec on hosts to run policies as code.
If you deploy cnspec to machines that can't download and install updates (because they're air-gapped or don't give cnspec write access), you must deploy cnspec providers. To learn more, read Manage cnspec Providers.
Installing cnspec using cloud-init
Most cloud environments support the configuration of an operating system during launch. In most cases cloud-init is used. For Linux systems, cloud-init supports bash scripts.
We simply leverage the Mondoo Bash installer script for cloud-init. To deploy agents with cloud-init, get an registration token via Mondoo Console -> Select Space -> Agents -> New Agent (➕Icon in action menu) and paste it into this snippet:
#!/bin/bash
export MONDOO_REGISTRATION_TOKEN='ey..gg'
bash -c "$(curl -sSL https://install.mondoo.com/sh)"
Once the machine is ready, the first scan will be performed about 30 seconds after the machine booted up.
Examples
AWS EC2 instance user data
-
Save the snippet shown above to
mondoo-cloudinit.shand paste in your registration token:Command Linecat > mondoo-cloudinit.sh << EOF
#!/bin/bash
export MONDOO_REGISTRATION_TOKEN='eyJhbG..bn'
bash -c "$(curl -sSL https://install.mondoo.com/sh)"
EOF -
Launch a new instance
Command Line# Note: you need to adapt the image-id, security-group-ids, key-name to your region and account
aws ec2 run-instances --region us-east-1 --image-id ami-0ad82a384c06c911e --security-group-ids sg-903004f8 --count 1 --instance-type t2.micro --key-name suki --user-data file://mondoo-cloudinit.sh
You can see the results of the vulnerability scan in your Mondoo Console once the installation is complete:
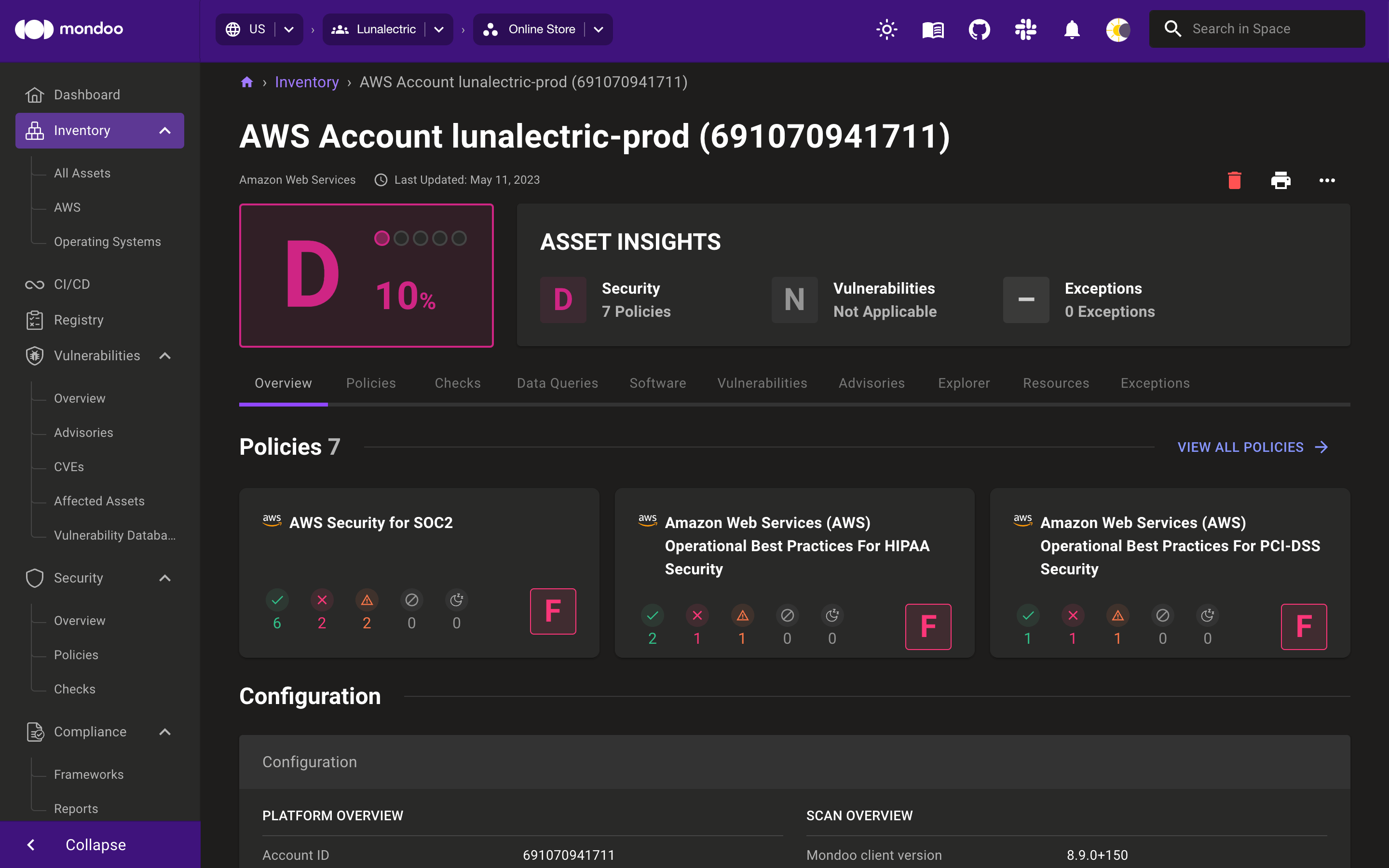
Once the machine is up and running, it will report vulnerabilities to Mondoo automatically. Further documentation for the AWS CLI is available at Launch, List, and Terminate Amazon EC2 Instances and Running Commands on Your Linux Instance at Launch
In case of troubleshooting, have a look at the /var/log/cloud-init-output.log to see the cloudinit run output.