Network devices are easy targets.We secure them for you.
Your team shouldn't spend hundreds of hours chasing network device misconfigurations, unpatched firmware, and EOL equipment. Mondoo's security experts continuously secure your network infrastructure — from vulnerability scanning through verified remediation — so you can focus on operations, not firefighting.






Why Network Device Security Is So Hard
Network devices are the backbone of every organization, yet they are consistently among the most neglected assets in security programs. The result: unpatched firmware, default credentials, misconfigurations, and EOL devices that attackers actively exploit.
CISA reports that network infrastructure devices are ideal targets for malicious actors because most organizational traffic must pass through them — yet they are rarely maintained at the same security level as servers and endpoints.
Source: CISA, Network Infrastructure Security Guidance
Default Credentials Left Unchanged
Factory settings and default passwords are often never changed after deployment. Attackers routinely exploit well-known default credentials to gain unauthorized access to routers, switches, and firewalls.
Firmware Patching Is Perpetually Delayed
Network teams postpone patches to avoid downtime and ensure stability. This creates a growing backlog of unpatched vulnerabilities that attackers can exploit to compromise your network infrastructure.
Configuration Complexity Breeds Errors
Network devices are inherently complex to configure. ACLs, routing policies, VPN tunnels, and firewall rules create thousands of potential misconfigurations that manual review can't keep up with.
EOL Devices Run Without Security Updates
End-of-Life devices are often left running for fear of disrupting operations. Without security updates, they become permanent vulnerabilities in your network that attackers can exploit with known CVEs.
How We Secure Your Network Devices
From day one, Mondoo's network security experts work as an extension of your team. Here's what the engagement looks like:
Discover Your Network Devices
We connect to your network infrastructure — Cisco, Palo Alto, Fortinet, and more — using agentless scanning powered by cnspec. No agents deployed, no impact on device performance.
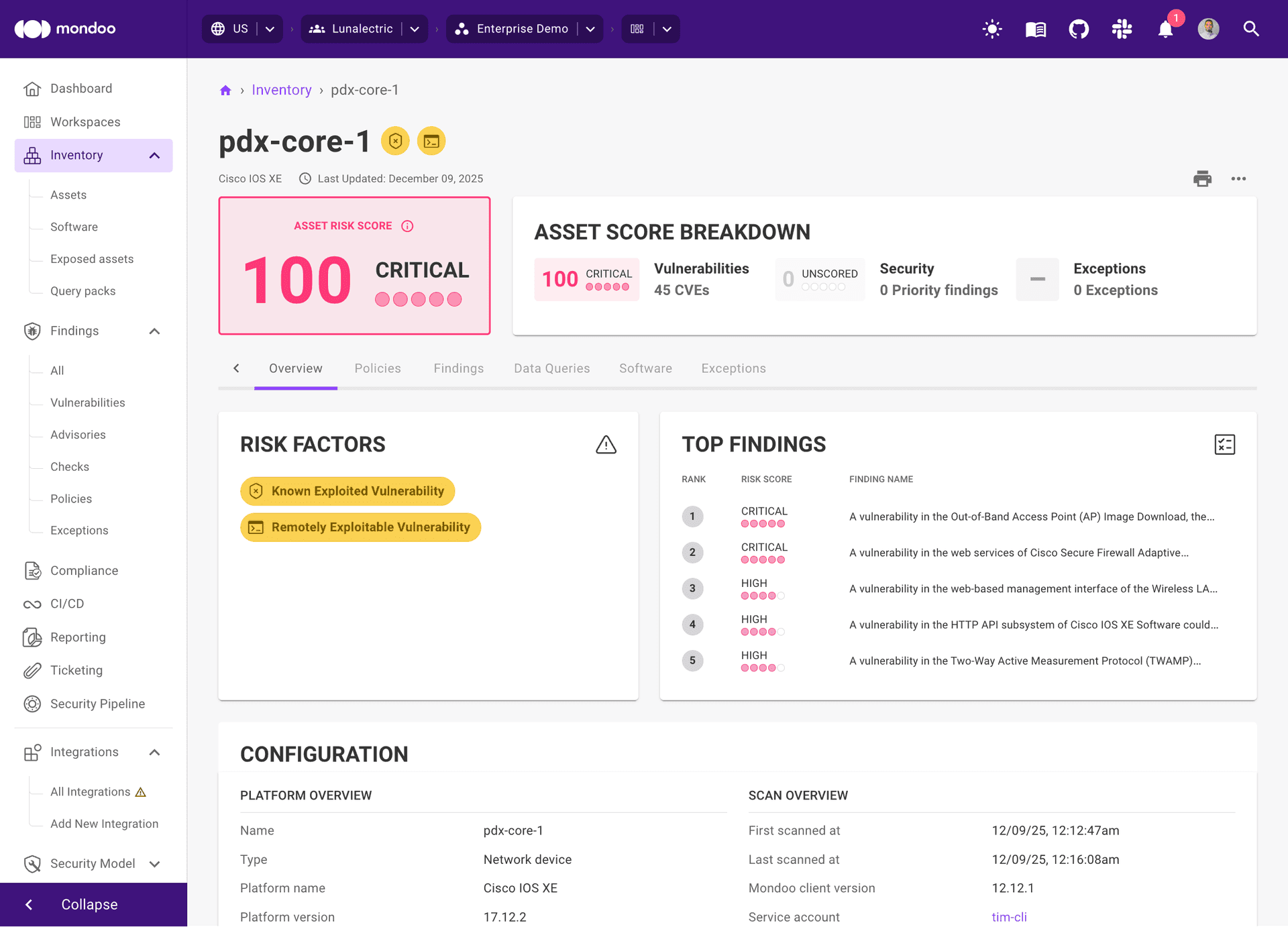
Assess Your Security Posture
We scan every device against CIS benchmarks, vendor hardening guides, and custom policies — identifying vulnerabilities, misconfigurations, default credentials, and EOL status across your entire fleet.
Prioritize by Real Risk
We triage findings by exploitability, exposure, and business impact. Critical vulnerabilities on internet-facing firewalls are escalated immediately. Low-risk findings on internal switches are deprioritized.
Deliver Verified Fixes
We create actionable remediation — firmware upgrade instructions, configuration changes, ACL corrections — delivered as tickets in Jira, ServiceNow, or your preferred ITSM tool with step-by-step guidance.
You Review and Approve
Your team reviews and approves all changes before they're applied. Nothing touches your network devices without your authorization. All access is least-privilege, all actions are logged and auditable.
Verify and Monitor
Mondoo rescans to confirm every remediation. Verified fixes close automatically. If configuration drift occurs, tickets are reopened. Ongoing monitoring catches new vulnerabilities as they emerge.
Your Dedicated Network Security Experts
Every engagement is led by experienced security professionals with deep expertise in network infrastructure, firewall management, and compliance frameworks. They understand Cisco IOS, Palo Alto PAN-OS, Fortinet FortiOS, routing protocols, and network segmentation at depth — and they operate as a seamless extension of your team.
You Retain 100% Control
We understand that giving external access to network infrastructure requires trust. Your team reviews and approves every change — via ITSM tickets, change advisory boards, or direct review. Nothing is remediated without your explicit authorization. All access is least-privilege, all actions are logged and auditable, and you maintain full visibility into everything we do.
Outcomes Our Customers Achieve
Real results from organizations that stopped managing network device security alone.
Reduction in Open Vulnerabilities
Customers see their vulnerability and misconfiguration backlog dramatically reduced within the first 90 days of engagement.
Faster Mean Time to Remediate
With dedicated experts handling triage, prioritization, and remediation guidance, critical network vulnerabilities are resolved in days, not months.
Faster Time to Compliance
Organizations achieve compliance with CIS benchmarks and frameworks like PCI DSS, NIS2, and SOC 2 significantly faster with continuous monitoring and expert guidance.
What our customers also report:
Many compliance frameworks require you to secure your network devices:
Trusted by Security Teams Worldwide
Organizations across industries trust Mondoo to secure their infrastructure.
“Mondoo gave us visibility we never had before. We went from guessing about our security posture to having clear, actionable data across our entire infrastructure.”
“Before Mondoo, vulnerabilities sat in our backlog for months. Now our dedicated team triages, prioritizes, and delivers fixes — we just review and approve.”
DIY Network Security vs. Mondoo
DIY Network Security
Mondoo Managed Service
Frequently Asked Questions
Stop chasing network vulnerabilities.
Let Mondoo's security experts continuously secure your network devices — from vulnerability scanning through verified remediation.




