Kubernetes security is complex.We handle it for you.
Your team shouldn't spend hundreds of hours chasing container misconfigurations and Kubernetes vulnerabilities. Mondoo's security experts continuously secure your containerized infrastructure — from cluster configuration through verified remediation — so you can focus on shipping, not firefighting.
Why Kubernetes Security Is So Hard
Kubernetes adoption is accelerating, but most organizations lack the specialized expertise and bandwidth to secure their container environments at scale. The result: growing backlogs of misconfigurations, unpatched vulnerabilities, and compliance gaps that put production workloads at risk.
Gartner estimates that more than 90% of global organizations will be running containerized applications in production by 2027 — yet most security teams lack dedicated container security expertise.
Source: Gartner, Top Strategic Technology Trends
Kubernetes Is Uniquely Complex
Multi-layer architecture spanning cloud infrastructure, cluster configuration, node management, workloads, and container images — each requiring specialized security controls that most teams don't have time to master.
Container Sprawl Outpaces Security
Teams spin up clusters faster than security can assess them. Ephemeral workloads, auto-scaling pods, and multi-cluster deployments create a constantly shifting attack surface that manual processes can't keep up with.
Compliance Gaps in Cloud-Native
CIS Kubernetes Benchmarks, NSA/CISA hardening guides, SOC 2, and NIST frameworks all require specific container security controls. Maintaining continuous compliance across dynamic Kubernetes environments is a full-time job.
Kubernetes Security Talent Is Scarce
Finding engineers who understand both Kubernetes operations and security at depth is extremely difficult. Most security teams are generalists stretched across too many priorities to specialize in container security.
How We Secure Your Kubernetes Environment
From day one, Mondoo's container security experts work as an extension of your team. Here's what the engagement looks like:
Onboard Your Clusters
We connect to your Kubernetes environments — EKS, GKE, AKS, OpenShift, or self-managed — and initiate continuous discovery of clusters, nodes, workloads, and container images.
Assess Your Security Posture
We scan your entire container infrastructure against CIS Kubernetes Benchmarks, NSA/CISA hardening guidelines, and custom policies — identifying misconfigurations, vulnerabilities, and compliance gaps across all five security layers.
Prioritize by Real Risk
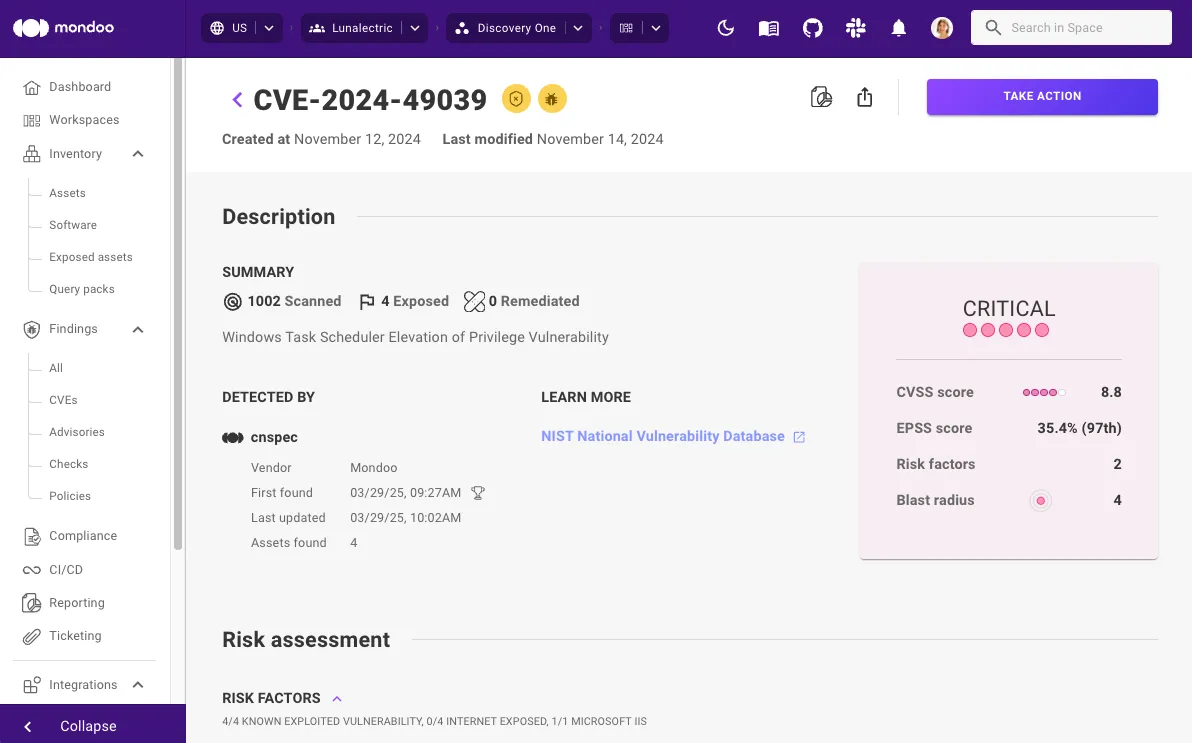
We triage findings by exploitability, exposure, and business context. Critical CVEs like container escapes (CVE-2022-0185), privilege escalations (Dirty Pipe, CVE-2022-0847), and actively exploited vulnerabilities are escalated immediately.
Deliver Verified Fixes
We create actionable remediation — RBAC configuration changes, network policy updates, image rebuild instructions, Helm chart patches — delivered as tickets in Jira, ServiceNow, or GitHub with step-by-step guidance.
You Review and Approve
Your team reviews and approves all changes before they're applied. You can approve via PR reviews, ITSM ticket approvals, or direct code deployment. Nothing touches your clusters without your authorization.
Verify and Monitor
Mondoo rescans to confirm every remediation. Verified fixes close automatically. If configuration drift occurs, tickets are reopened. Ongoing monitoring catches new vulnerabilities as they emerge.
Your Dedicated Kubernetes Security Experts
Every engagement is led by experienced security professionals with deep expertise in Kubernetes operations, cloud infrastructure, and compliance frameworks. They understand container runtimes, pod security standards, RBAC models, and network segmentation at depth — and they operate as a seamless extension of your team, not a disconnected outsourcer.
You Retain 100% Control
We understand that giving external access to production Kubernetes clusters requires trust. Your team reviews and approves every change — via pull requests, ITSM tickets, or direct code review. Nothing is remediated without your explicit authorization. All access is least-privilege, all actions are logged and auditable, and you maintain full visibility into everything we do.
Outcomes Our Customers Achieve
Real results from organizations that stopped managing container security alone.
Reduction in Open Vulnerabilities
Customers see their vulnerability and misconfiguration backlog dramatically reduced within the first 90 days of engagement.
Mean-Time to Remediation
Critical container vulnerabilities and Kubernetes misconfigurations are resolved in days, not months — without burdening your team.
Faster Than Doing It Yourself
Free your team from hundreds of hours of manual Kubernetes security triage, configuration hardening, and verification work.
Beyond the Numbers
The Kubernetes Threats We Protect You From
Attackers exploit vulnerabilities across every layer of Kubernetes. Mondoo's experts continuously monitor, detect, and remediate these attack vectors across your entire container environment.
What Your Cluster Faces
What Your Cluster Faces
What Mondoo's Team Delivers
Outdated Kubernetes Versions
Running end-of-life Kubernetes versions exposes clusters to known, exploitable vulnerabilities. CVE-2021-25741 allowed path traversal in Kubernetes, enabling access to files outside mounted volumes.
What Mondoo's Team Delivers
Mondoo's experts continuously monitor your cluster versions and proactively escalate end-of-life releases, ensuring patches are prioritized and remediated before they become exploitable.
Insecure Communication
Improperly configured TLS between Kubernetes components enables man-in-the-middle attacks. The ArgoCD authentication bypass (CVE-2022-24348) exploited insecure communication to gain cluster access.
What Mondoo's Team Delivers
Our team validates TLS certificate configurations, secure communication protocols, and API server settings across all cluster components — and delivers fixes for any gaps found.
Inadequate Access Controls
Overly permissive RBAC configurations are one of the most common Kubernetes security failures. Attackers exploit excessive permissions to escalate privileges and move laterally across the cluster.
What Mondoo's Team Delivers
Mondoo's experts audit your RBAC configurations against the principle of least privilege, identify overly permissive roles and bindings, and deliver specific policy changes to lock down access.
Insufficient Network Segmentation
Without proper network policies, any compromised pod can communicate with every other pod and the control plane — enabling lateral movement and data exfiltration.
What Mondoo's Team Delivers
We assess your network policies and namespace isolation, then deliver Kubernetes NetworkPolicy configurations that enforce proper segmentation between control plane, workloads, and namespaces.
Insecure Pod Configurations
Privileged containers, root access, unnecessary capabilities, and plaintext secrets are the leading causes of container breakouts. The CRI-O escape (CVE-2022-0811) allowed kernel parameter injection from a pod.
What Mondoo's Team Delivers
Mondoo scans all workload configurations against Pod Security Standards and CIS benchmarks, then delivers specific YAML patches to eliminate privileged escalation paths and enforce security contexts.
Vulnerable Container Images
Outdated base images with known CVEs, embedded secrets, and malicious packages in public registries compromise entire clusters. Crypto-mining attacks frequently target unpatched container images.
What Mondoo's Team Delivers
Our team continuously scans your container images across all registries for CVEs, malware, and misconfigurations — both pre-deployment in CI/CD and at runtime — and escalates critical findings with rebuild instructions.
What Mondoo's Team Handles at Every Layer
Kubernetes security spans five distinct layers — each requiring specialized expertise. Mondoo's experts manage security across all of them, so your team doesn't have to.
Cloud Services
Mondoo's team secures the underlying cloud infrastructure — reviewing security groups, IAM roles, networking configurations, and cloud provider settings that your Kubernetes clusters depend on.
Cluster Configuration
Our experts harden cluster-level settings including API server configuration, etcd encryption, admission controllers, Pod Security Standards, and audit logging — aligned to CIS benchmarks and NSA/CISA guidelines.
Cluster Nodes
Mondoo's team manages node patching, container runtime hardening, Kubelet configuration review, and EOL OS replacement across your fleet — with verified remediation after every change.
Workloads
We review and harden deployments, replication controllers, and pods — eliminating privileged containers, enforcing resource limits, securing service accounts, and validating pod security contexts.
Application Containers
Our team continuously scans container images for CVEs and misconfigurations, identifies outdated base images, and provides rebuild guidance — reducing your attack surface at the application layer.
Works Across Every Major Kubernetes Distribution
Mondoo works with your existing Kubernetes environment — no rip-and-replace required. We support all major distributions and managed services:
Trusted by Security Teams Worldwide
Trusted by 300+ customers worldwide, including Fortune 50 companies and enterprises around the globe.
“With Mondoo we can see vulnerability data and perform queries from a single platform, which allows us to make better and faster decisions.”
“Mondoo was a godsend for us. Having a tool like this helps small cyber teams wear multiple hats.”
DIY Container Security vs. Working with Mondoo
Doing It Yourself
Working with Mondoo
Frequently Asked Questions
Ready to Secure Your Kubernetes Environment Without Adding Headcount?
Let Mondoo's experts manage your container security end-to-end. Get a free security assessment and see what we can fix in the first 30 days.