
Our Technology
The technology powering
your security service
Mondoo's platform is the engine behind our Managed Agentic Vulnerability Management Service. It's how our experts and AI agents scan your infrastructure, prioritize what matters, and deliver remediation code, all from a single unified system.
300+
Organizations trust Mondoo
60%
Average vulnerability reduction
100+
Integrations across your stack
Why This Technology Matters
Built to deliver results, not dashboards
Most security tools generate alerts you have to act on yourself. Mondoo's platform was purpose-built to power a managed service that actually fixes things.
Unified
One platform for cloud, on-premises, SaaS, endpoints, network devices, and the SDLC. Our service team operates it for you, replacing 5-10 siloed tools with complete visibility.
AI-Native
Our patented AI model maps relationships between assets, configurations, and vulnerabilities, enabling our agents to make fast, accurate remediation decisions.
The Problem We Solve
Siloed tools create blind spots
Most organizations run 5-10 separate security tools that don't talk to each other. Cloud scanners miss on-prem. Vulnerability scanners lack configuration context. The result: fragmented visibility and critical gaps that put your business at risk.
One platform, complete visibility
Single view across cloud, on-prem, SaaS, endpoints, network devices, and the SDLC
Correlated findings with full asset and configuration context
Continuous monitoring with real-time drift detection
One policy engine, one query language, one remediation workflow
What We Scan
Your entire IT infrastructure, covered
Mondoo's platform scans cloud, on-prem, SaaS, endpoints, network devices, and your software development lifecycle, all from a single system with the same depth of coverage everywhere.
Cloud Security
AWS, Azure, GCP, OCI
On-Prem Security
Physical workloads and servers
Network Device Security
Firewalls, switches, routers
Endpoint Security
On-prem and remote endpoints
SaaS Security
Business-critical SaaS applications
SDLC Security
Shift-left security in pipelines
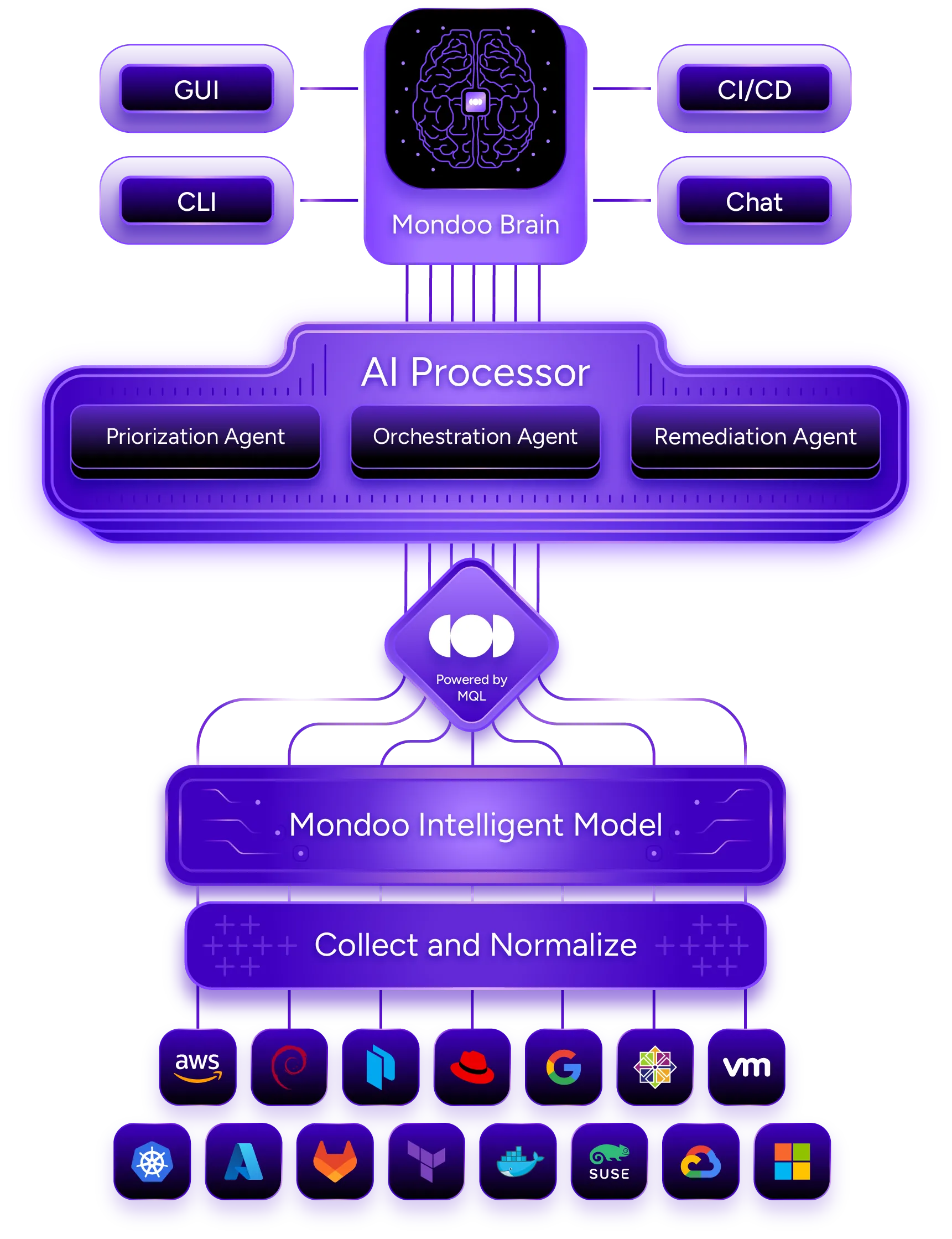
AI-Native Architecture
The Mondoo Intelligent Model
Our patented Mondoo Intelligent Model maps the hidden relationships between assets, configurations, and vulnerabilities across your infrastructure. This is how our AI agents make fast, accurate decisions based on deep contextual understanding rather than isolated data points.
Contextual Understanding
The platform graphs how vulnerabilities relate to configurations, assets, and business impact, so our team always knows what to fix first.
Risk-Based Prioritization
AI agents analyze full context, exploitability, exposure, and business criticality, not just CVSS scores.
Integrated Into Your Stack
Results flow into your existing tools: GUI dashboards, CLI, CI/CD pipelines, Jira, ServiceNow, Slack, and more.
How It Works
From discovery to verified fix in five steps
This is the workflow our experts and AI agents execute on your behalf, continuously, across your entire infrastructure.
Discover
Continuous asset discovery across cloud, on-prem, SaaS, network devices, endpoints, and your SDLC.
Scope
Custom workspaces, asset tagging, SLAs, and compliance framework mapping tailored to your business.
Prioritize
AI risk scoring using CVSS, EPSS, exploitability, and business impact, not just severity numbers.
Fix
Remediation code, pull requests, and ITSM tickets delivered directly into your workflow.
Report
Progress tracking, compliance reporting, and MTTR measurement for your leadership team.
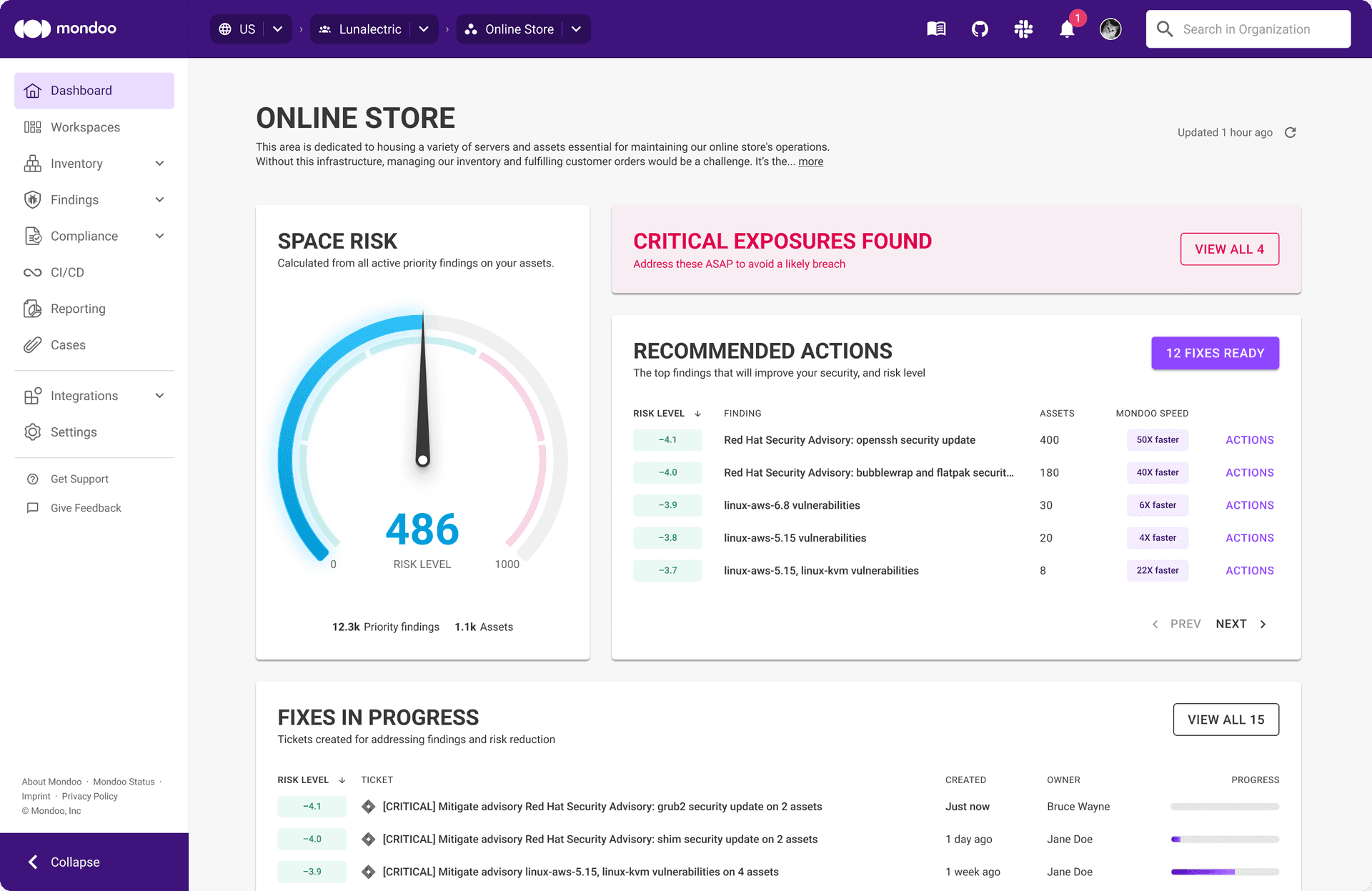
Platform Capabilities
What the technology does for you
Every capability below is operated by Mondoo's service team, so you get the results without having to run anything yourself.
Centralized Findings
One unified, prioritized view of all your assets and vulnerabilities. No more switching between consoles or deduplicating alerts across tools.
Risk-Based Prioritization
AI-powered risk scoring that weighs exploitability, exposure, and business context so our team focuses on what matters most to your organization.
Continuous Compliance
300+ compliance templates and CIS benchmarks with automated evidence collection. Always audit-ready without the manual overhead.
Remediation Code Delivery
Pre-tested code snippets, pull requests, and ITSM tickets in Jira, ServiceNow, or GitHub. Fixes delivered to your workflow, not just advisories.
Agentic Patching
AI agents autonomously create pull requests, generate Ansible/Terraform playbooks, and apply fixes with your approval.
Executive Reporting
Scheduled compliance reports, vulnerability trend tracking, MTTR metrics, and SLA dashboards for leadership visibility.
Frequently asked questions
The Mondoo Difference
Teams reduce daily security review time from
"3+ hours sifting through 15 tools"
to
"Less than 10 minutes"
Get a Free Security Assessment