Mondoo 8.1 is out!
🥳 Mondoo 8.1 is out! This release includes policy variants, new security policies, and more!
Get this release: Installation Docs | Package Downloads | Docker Container
🎉 NEW FEATURES
Policy variants
Sometimes queries differ slightly when executed in different environments. This can happen with:
-
Highly related queries, like OS checks that run differently on physical servers than they do on containers
-
Queries that test for similar things on entirely different targets
Let's take a look at the latter example:
queries:
- uid: no-public-ip
title: No public IPs are allowed on internal instances
variants:
- uid: no-public-ip-aws
- uid: no-public-ip-terraform-aws
- uid: no-public-ip-aws
mql: |
aws.ec2.instances.all( publicIp == "" )
filters: |
asset.platform == "aws"
- uid: no-public-ip-terraform-aws
mql: |
terraform.resources.
where( nameLabel == "aws_instance" ).
all( arguments['associate_public_ip_address'] != true )
filters: |
asset.platform == "terraform-hcl"
This query ensures that “No public IPs are allowed on internal instances.” This query is implemented in two different ways: one for the AWS API (no-public-ip-aws) and one for Terraform (no-public-ip-terraform-aws). You can run this check against both AWS accounts and Terraform files and get consistent reporting.
Additionally, this addresses a common use case where there's a split between things that happen in development and things that run in production. If you have separate tools in different environments, or even separate policies, you previously had to manage exceptions to certain checks across both ends of the lifecycle. Now with variants, you can instead define exceptions on the combined check, making sure that they are treated consistently between development and production.
New Okta Security policy + MQL enhancements
Last week we shipped continuous Okta scanning integration in the Mondoo Console. This week we have a new Mondoo security policy and improvements to Okta MQL resources so you can secure your Okta environment in just minutes.
Our new Okta Security Policy by Mondoo includes 11 checks to keep your Okta environment secure out of the box:
- Ensure MFA is active for everybody accessing Okta platform
- Ensure a limited session lifetime has been enforced
- Ensure OpenID or SAML authentication is used for app access
- Ensure normal users cannot unlock themselves
- Ensure Secure Web Authentication (SWA) is disabled for critical apps
- Ensure the option "at every sign-in" is enabled for MFA
- Ensure "Persist session cookies across browser sessions" is disabled
- Ensure the users with Super Admin rights are limited to 3
- Ensure the strong factor is used for MFA
- Ensure that MFA is configured to use password/IdP plus another authentication factor
- Ensure the "Password/IdP plus Another" factor is chosen for MFA
If you want to define your own business policies for Okta, you're in luck. We've improved our Okta MQL policies, giving your access to more information on your environment:
- Gather
okta.roleanduser.roles, allowing you to query which roles are assigned to a user - Gather access policy rules
- Fix
okta.trustedOrigin.scopesparsing
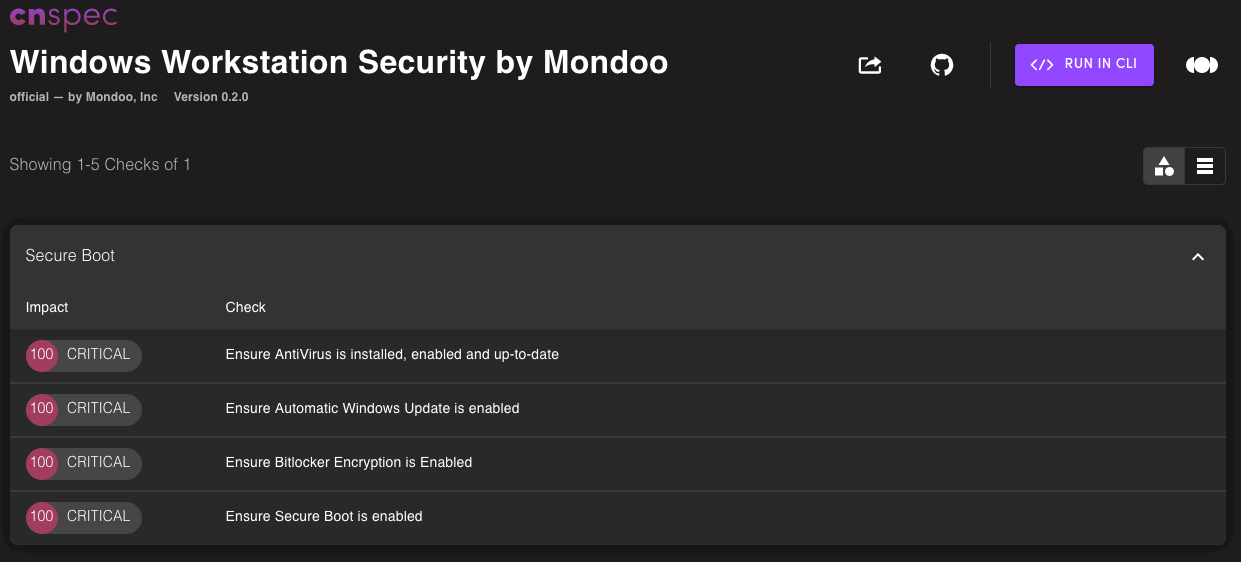
New Microsoft Workstation Security policy
Our all-new Microsoft Workstation Security policy provides security guidance for workstations running Windows 10 and 11.
New and updated Kubernetes policies
Kubernetes moves fast, so ensuring your security policy matches the latest and greatest security recommendations is essential. Mondoo now includes the latest CIS benchmarks for Kubernetes distributions with updated auditing and remediation steps as well as new checks for the control plane in cloud distributions:
- New: CIS Kubernetes V1.24 Benchmark 1.0
- Updated: CIS Amazon Elastic Kubernetes Service (EKS) Benchmark 1.2
- Updated: CIS Google Kubernetes Engine (GKE) Benchmark 1.3
- Updated: CIS Azure Kubernetes Service (AKS) Benchmark 1.2
- Updated: CIS Red Hat OpenShift Container Platform v4 Benchmark 1.1
🧹 IMPROVEMENTS
Smaller installation size
The Mondoo package has been optimized to reduce the space on disk consumed by Mondoo, cnquery, and cnspec commands. The legacy Mondoo CLI is now 200MB smaller on all platforms. Additionally, the cnquery and cnspec CLIs are each ~150MB smaller on Windows systems.
More AWS ElasticCache data in MQL
We've deprecated aws.elasticache.clusters in favor of a new aws.elasticache.cacheClusters resource that presents cluster data in an easier to consume format.
cnquery> aws.elasticache.cacheClusters { * }
aws.elasticache.cacheClusters: [
0: {
arn: "arn:aws:elasticache:us-east-1:ID:cluster:vjtest-001"
notificationConfiguration: ""
cacheSubnetGroupName: "vjtest"
atRestEncryptionEnabled: false
logDeliveryConfigurations: []
ipDiscovery: "ipv4"
authTokenLastModifiedDate: null
numCacheNodes: 1
engine: "redis"
networkType: "ipv4"
region: "us-east-1"
securityGroups: []
transitEncryptionMode: ""
cacheNodeType: "cache.t3.medium"
engineVersion: "7.0.7"
preferredAvailabilityZone: "us-east-1c"
transitEncryptionEnabled: false
cacheClusterId: "vjtest-001"
authTokenEnabled: false
snapshotRetentionLimit: 0
Expanded Azure Security policy
We've updated the Microsoft Azure Security by Mondoo policy with seven new checks to keep your Azure environment secure out of the box:
- Ensure that App services can authenticate with Active Directory
- Ensure that Web App takes advantage of latest version of TLS encryption
- Ensure that the expiration date is set for all keys and secrets in key vaults
- Ensure it is possible to recover key vaults
- Ensure all operations on key vault are logged
- Ensure that activity log alerts exist for the commands Create, Update, and Delete Network Security Group
- Ensure that "Notify about alerts with high severity" is enabled
Expanded Google Workspace policy
We've updated our Google Workspace Security by Mondoo policy with three new checks:
- Ensure more than one user has Super Admin permissions
- Users should not be allowed less secure app access
- Super users should use hardware-based security keys
Remove v7 deprecations
Now that v8 is out, we've cleaned up several old flags and options that were deprecated during v7.
Deprecated GCP flags
We removed the deprecated cnspec and cnquery flags for GCP --project and --organization. We also marked the --project-id and --organization-id flags as deprecated. Use cnspec scan gcp organization MY_ORG or cnspec scan gcp project MY_PROJECT instead.
Deprecated K8s flag
We removed the deprecated cnspec and cnquery Kubernetes --namespace flag. Use --namespaces instead.
Deprecated Azure/Microsoft 365 inventory options
We removed the deprecated tenantId, clientId, and subscriptionId Azure/Microsoft 365 inventory file configuration options. Use tenant-id, client-id, and subscription-id instead.
Deprecated azure.subscription.sqlService.database fields
We removed the deprecated containmentState, currentServiceObjectiveId, requestedServiceObjectiveId, and serviceTierAdvisors fields from the azure.subscription.sqlService.database resource.
🐛 BUG FIXES AND UPDATES
- Don't fail an entire AWS account scan when a single service has a region restriction set.
- Fail better when a Kubernetes namespace cannot be scanned due to permissions failures.
- Fix
cnspec bundle formatfailure introduced in 8.0. - Update the scanning progress bar to make it more clear when an asset was not scored.
- Fix console login page text field text color to be black.
- Fix console login page links to user agreement and privacy policy to load in new windows.
- Don't display
0 Othersfor Azure assets in the fleet page. - Fix off-center spinner loaders on the integration pages.
- Rename "Latest Advisories" on the overview page to be "Top Advisories" to better match what the widget shows.
- Show accurate billing plan data in the console.
- Improve rendering on the welcome page on small displays.
